Streaming
Service overview
The service enables online broadcasting through the internet without the need to purchase and configure your own servers. Broadcasts are distributed through a CDN network, ensuring content delivery to viewers from the nearest server.
Key features:
- HTML5 player: A ready-to-use solution for viewing broadcasts that easily integrates with any website and works on all modern devices
- Adaptive streaming: Automatic broadcast quality adaptation based on connection speed and viewer device capabilities
- Popular protocol support: Works with RTMP, RTSP, and SRT for maximum compatibility with various equipment
- Recording and DVR: Ability to save broadcasts and organize time-shifted viewing
- Security: Flexible content access settings
Creating a Broadcast
- Go to the Streaming section in your personal account
- Click "Create live streaming" in the top right corner
- Choose the stream delivery method:
- Pull - we pull your stream via RTMP, RTSP, SRT, and HLS over HTTP/HTTPS.
- Publish - you send the stream to our servers (RTMP/RTSP or SRT)

When choosing the publishing method, consider your equipment capabilities and broadcast requirements. RTMP/RTSP is suitable for most cases, SRT provides more reliable transmission with unstable connections, and HLS Pull is convenient if the stream already exists in the required format.
Attention!
System limits:
- Maximum 100 broadcasts per account
- Up to 10 streams for RTMP/RTSP/SRT publishing within one broadcast
Contact support to increase these limits.
Preparing for Broadcast
For the "Publish" delivery method, you'll need special software - an encoder that supports RTMP, RTSP or SRT protocols. We recommend selecting and configuring a suitable encoder in advance. Detailed instructions for configuring popular encoders are available in the corresponding documentation section here.
Please note
When using the RTSP streaming protocol, it's recommended to disable B-frames in the video encoding settings. This will help avoid possible artifacts in the final video stream.
Broadcast Configuration
RTMP/RTSP-publish
Connection Setup
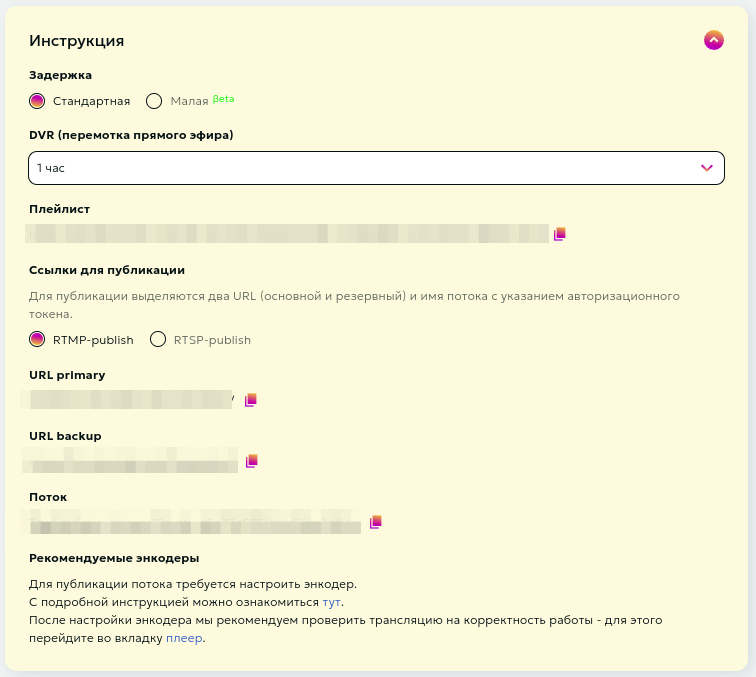
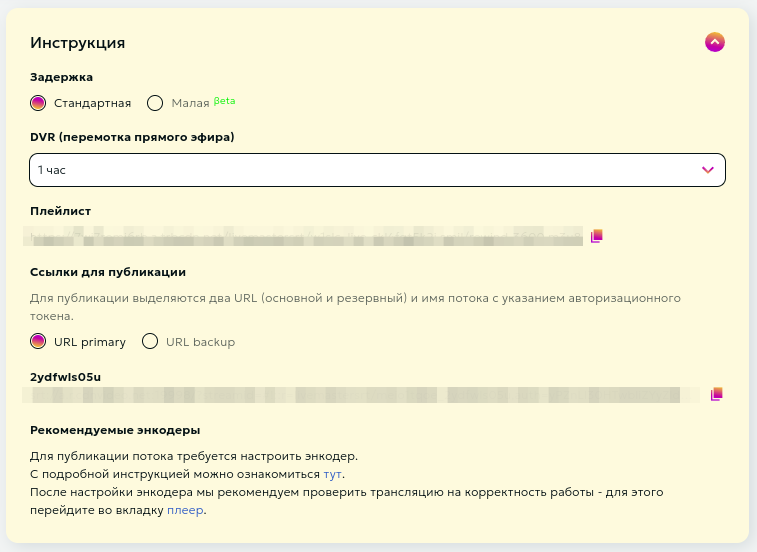
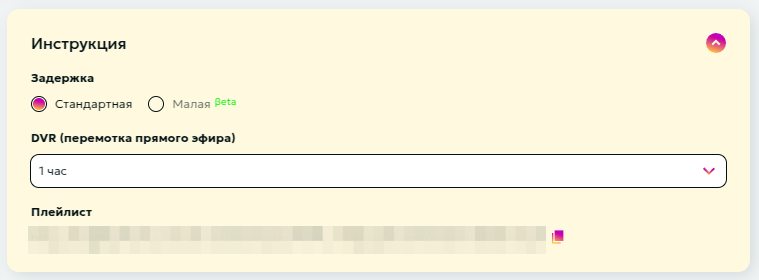
The "Instructions" section contains all necessary data for starting a stream:
- Stream latency selection
- DVR (playback) depth selection
- Publishing and viewing stream links
You can select the stream latency:
- Standard - optimal mode for most streams
- Low - reduced latency (most viewers will experience less than 10 sec latency)
DVR (playback) is the ability to rewind a stream even while it's live. Viewers can start watching from the beginning or return to missed moments. DVR is available for streams with standard latency. You can select the DVR depth from the dropdown menu. Maximum depth is 12 hours.
The system automatically generates necessary publishing data:
- Publishing URLs (primary and backup)
- Unique stream key
The backup URL is recommended when sufficient bandwidth is available - this ensures additional stream reliability. For publishing multiple quality levels in some encoders (e.g., Wirecast), streams need to be specified separately.
Videoplayer
After receiving publishing links and configuring the encoder, we recommend testing the stream for proper operation.
You can view your stream on the stream editing page in the player block.

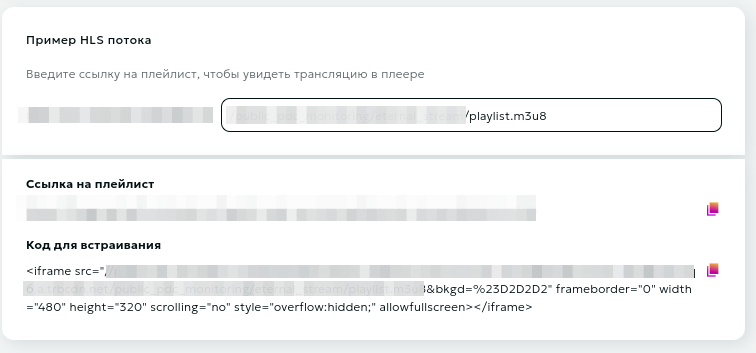
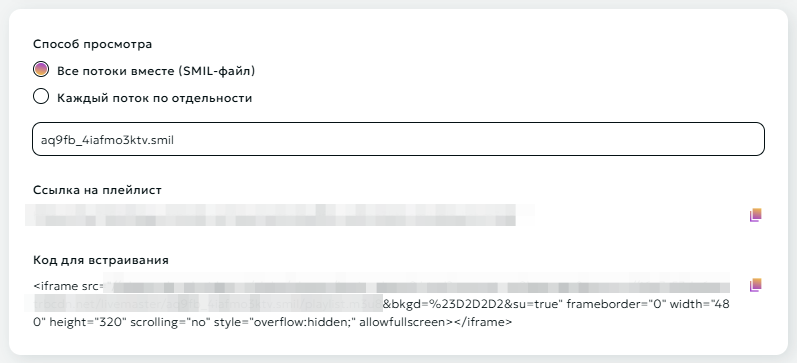
Clicking the "Configure" button under the player will redirect you to the player settings page, where you can choose your preferred viewing method: viewing created streams separately or all streams together in one player. Below the viewing method selection form, you can find the playlist link and code for embedding the player on your web page.
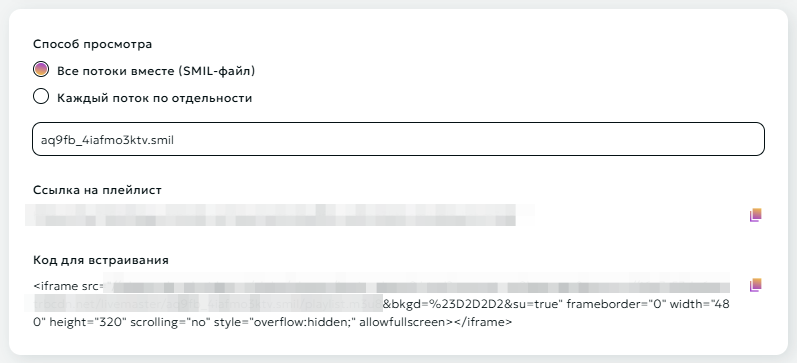
Attention
Use the "Code for embedding" frame to place the player on your resource.
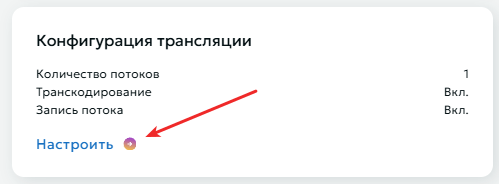
Streaming configuration
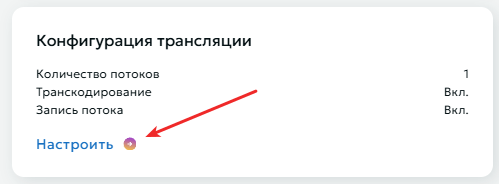
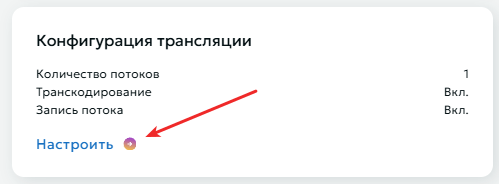
Advanced broadcasting settings are available in the "Streaming configuration" block.
Stream Settings
You can create up to 10 streams of different quality
- Open the "Streaming configuration" section
- Use the "Add Stream" button to create a new stream
- For each stream specify:
- Clear name for easy management
- Resolution from the provided list
- Remove unused streams if necessary
- Save changes after configuration

Transcoding $
Transcoding is necessary for creating multibitrate streams. As output, you get several streams of different quality, allowing users to manually select their preferred option or leave adaptive streaming, which automatically adjusts based on the user's bandwidth. This eliminates buffering issues for viewers with slow internet and improves user experience.
To configure transcoding:
- Select appropriate transcoding package
- Save settings
To deactivate transcoding, click again on your selected transcoding package, then click the "Save" button at the bottom of the page.
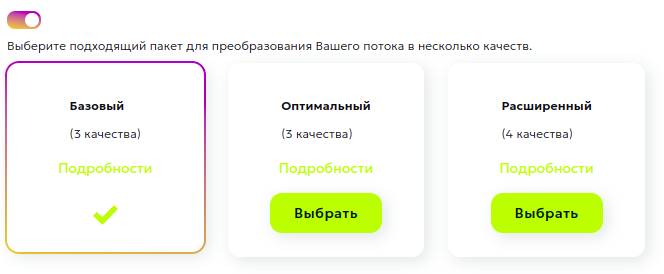
Important transcoding considerations:
- Only one input stream can be used
- Various packages with different processing parameters are available
- The system will automatically create streams of different quality
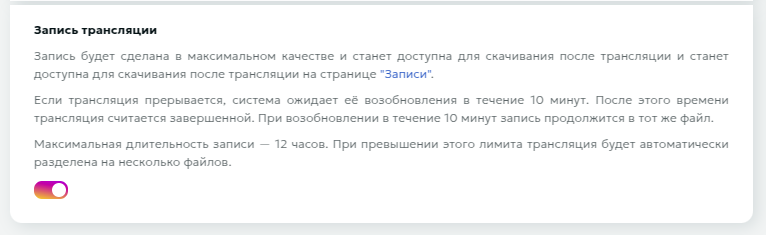
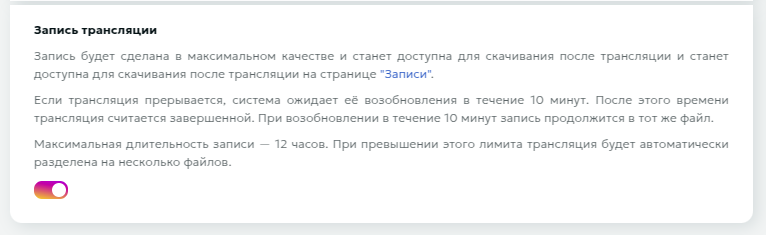
Stream Recording $
The Stream Recording feature enables archiving of live broadcasts for subsequent use.
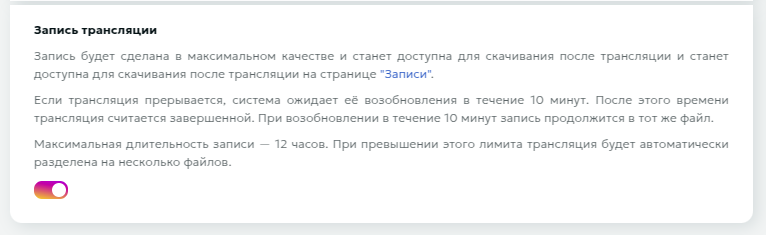
Key Features:
- Automatic selection of maximum available quality
- Downloads accessible via the Records page
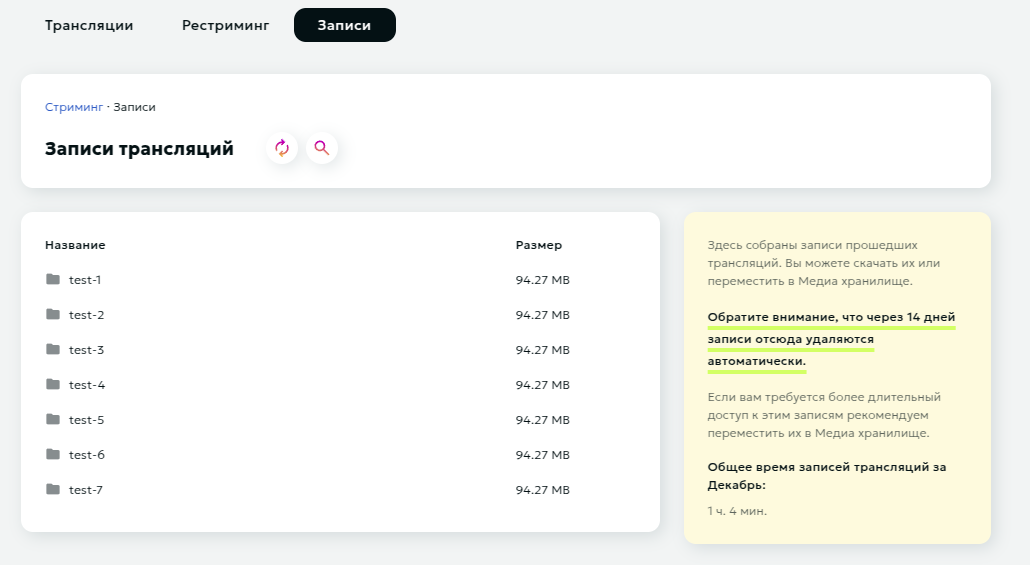
- 14-day retention period for records
- Option to transfer to Media Storage for extended retention and processing
Operational Flow:
- Activate the recording switch in stream settings
- Recording initiates automatically upon stream detection
- Stream Interruption Protocol:
- System maintains 10-minute reconnection window
- Recording continues to same file if stream resumes within window
- Stream designated as complete after 10-minute timeout
Attention
- Single record file capacity: 12 hours. System automatically generates new file upon reaching capacity
- Default retention period: 14 days from creation
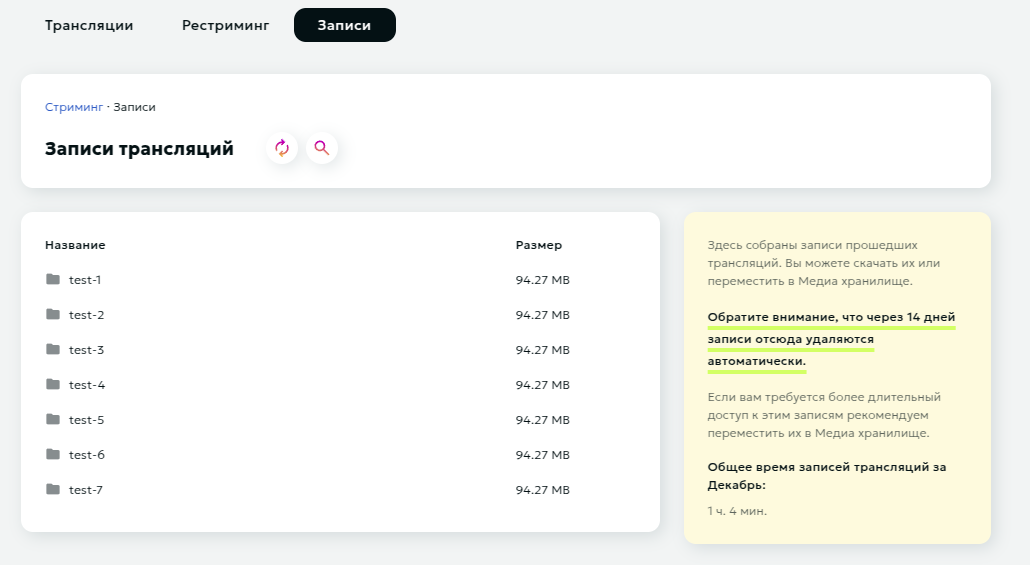
Records Management Interface
The Records page provides access to recorded streams and essential reference information.
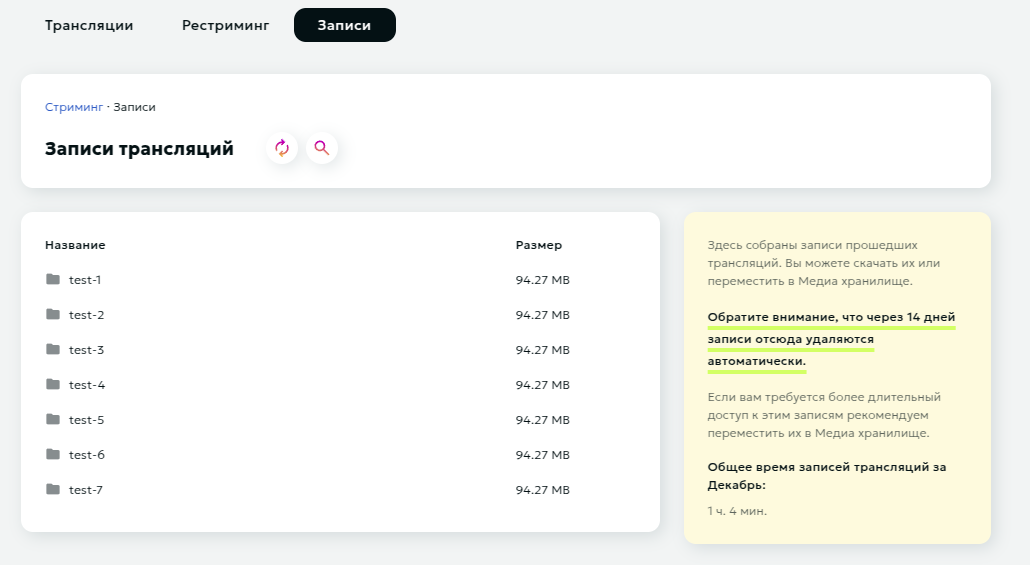
Interface functionality includes:
- Comprehensive record content viewer
- File download capability
- Media Storage transfer function
- Monthly recording usage metrics
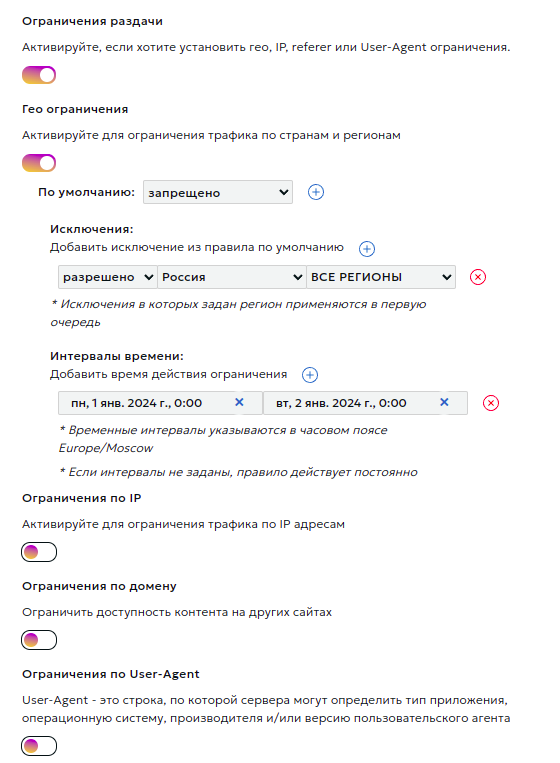
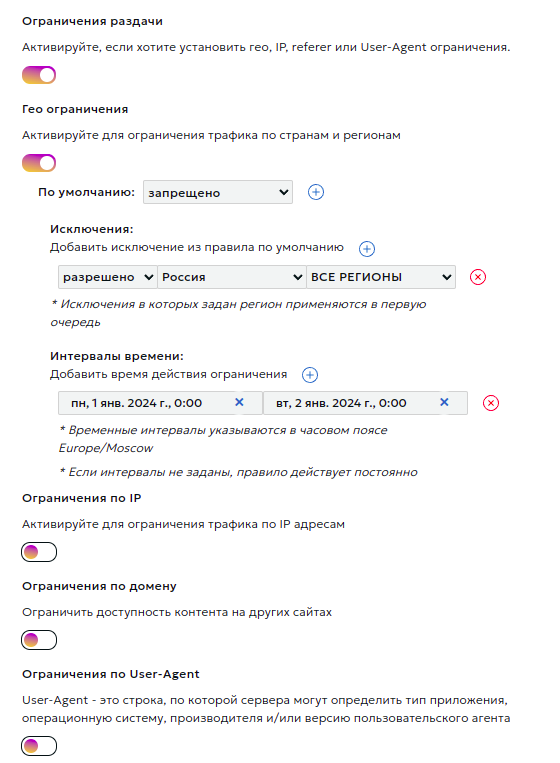
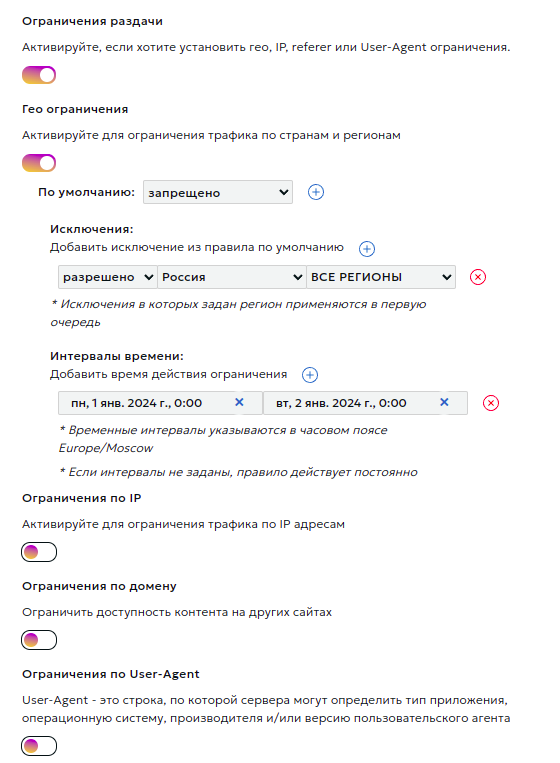
Content Access Restrictions $
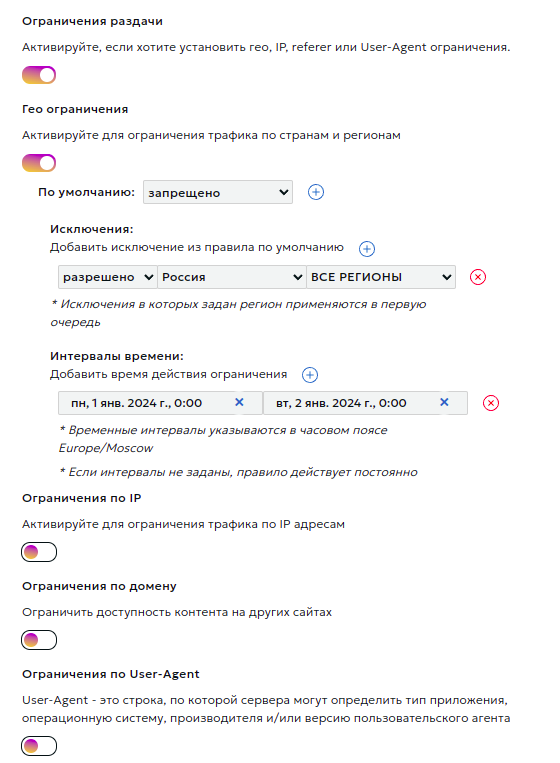
In this section, you can set content distribution restrictions based on:
- Country and region
- IP address
- Referer
- User-Agent
- Authorization restrictions
Module Configuration Process
- Activate the type of restriction you need and choose the default rule (deny or allow).
- Add exceptions to the default rule. For geo-restrictions, also select a rule for the exception itself. This way, you can, for example, deny traffic for an entire country while allowing it for a specific region.
- If necessary, set time intervals for the rule's validity. Intervals should not overlap.
- It's possible to add several different rules of each type, provided their time intervals do not overlap.
Authorization by Secret Key
Description:
Authorization of user requests is performed exclusively in the CDN network, external resources are not used. The decision to access a stream is made by means of our network based on the criteria specified by the content owner:
- Secret key. It is checked that the link was generated by the content owner.
- The URI of the requested stream. It is checked that the link was generated specifically for this stream.
- User's IP address (optional). It is checked that the stream was requested from exactly the IP address for which the link was generated. You can disable the check by selecting the "Do not impose IP address filter" option.
- The expiration time of the link (optional). You can turn off the check by selecting the "Do not impose time restrictions" option.
At the moment the user accesses a protected stream, the content owner needs to generate a special link.
Example:
http://example.a.trbcdn.net/md5(HucJ8tJFjy97yuox2OycOQ,1704067200)/path/to/stream/playlist.m3u8
The link contains authorization parameter md5(<md5 hash>[,<expires>]):
<md5 hash>- MD5 hash in Base64 format for URL, generated based on secret key, URI of the requested stream, user's IP address (optional) and link lifetime (optional);<expires>is the expiration time of the link in POSIX time format (optional).
When accessing content using the generated link, the CDN calculates the MD5 value and compares it with the received one.
If the MD5 value does not match, then a 403 Forbidden response is returned to the user (access is denied).
If the current time exceeds the value <expires>, then a response with the code 410 Gone (the target stream is no longer available) is returned to the user.
Algorithm for generating an MD5 hash (<md5_hash>) for signing links:
- Form the signature string
<secret_word><path_to_stream><ip><expire_time>. The<ip>and/or<expire_time>elements are not added to the signature string ifDo not impose IP address filterand/orDo not impose time restrictionsis specified in the local authorization settings. - Generate
base64_urlviabase64_url(md5(<signature string>)). - Generate the
<md5 hash>signature by performing the following substitutions inbase64_url:- replace the
=character with the empty string''. - replace the
+character with- - replace the
/character with_
- replace the
- Form the link using the obtained signature
<md5 hash>.
Attention
- The domain part of the URI is not used when calculating the hash!
- You can sign part of the path (for example, for /path/to/stream, you can sign the stream itself, /path/to, /path)
- When generating MD5, the URL should not contain urlencoded characters, but should contain the original characters: cyrillic, spaces, percentages, etc. Then you should request the urlencoded version of the URL with this hash.
- The MD5 hash calculated for HTTP is the baseline for this stream. The same hash will be used for links to a stream over the HTTP, HTTPS protocols, despite the fact that the URI for different protocols may differ slightly.
Example of link generation:
-
There are the following input data:
- Secret key:
zah5Mey9Quu8Ea1k - User IP address:
1.2.3.4 - Stream URI:
http://example.a.trbcdn.net/path/to/stream/playlist.m3u8 - Expiration time of the link:
1704067200
- Secret key:
-
Form the signature string
<secret_word><path_to_stream><ip><expire_time>. Let's assume that we include both IP address and link expiration time.Then the signature string looks like this:
zah5Mey9Quu8Ea1k/path/to/stream1.2.3.41704067200 -
Generate
<md5 hash>:PHP example:
$ php -r 'print str_replace("=", "",strtr(base64_encode(md5("zah5Mey9Quu8Ea1k/path/to/stream1.2.3.41704067200", TRUE)), "+/", "-_")) . "\n";' HucJ8tJFjy97yuox2OycOQ#!/usr/bin/python3 import base64 import hashlib secret_word = 'zah5Mey9Quu8Ea1k' path = '/path/to/stream' ip_address = '1.2.3.4' expiration_timestamp = 1704067200 def generate_local_signature(secret_word, path, ip_address=None, timestamp=None): string_to_sign = f'{secret_word}{path}' if ip_address is not None: string_to_sign = f'{string_to_sign}{ip_address}' if timestamp is not None: string_to_sign = f'{string_to_sign}{timestamp}' hashed_string = hashlib.md5(string_to_sign.encode()).digest() decoded_base64_string = base64.b64encode(hashed_string).decode() local_signature = decoded_base64_string.replace('+', '-').replace('/', '_').replace('=', '') return local_signature print(generate_local_signature(secret_word, path, ip_address, expiration_timestamp)) # HucJ8tJFjy97yuox2OycOQPython example:
-
Result link:
http://example.a.trbcdn.net/md5(HucJ8tJFjy97yuox2OycOQ,1704067200)/path/to/stream/playlist.m3u8
External Script Authorization
External authorization is designed to be able to restrict access to the stream with custom logic described in your authorization script. A decision to access the stream is made based on response of your script.
If the authorization script responded with status code = 200, then access to the stream is allowed. Otherwise, access is denied.
The following headers are passed to the authorization script:
- Host: contains the domain name of the server for which the request is intended;
- X-Request-URI: contains the URI of the requested stream;
- X-Forwarded-For: contains the real IP address of the user;
- X-Remote-Addr: contains the IP address of the user or the proxy server.
DVR (Live Stream Playback)
The DVR reset (button "Reset stored DVR") allows clearing the accumulated stream buffer and starting to form it anew. During reset, all previously accumulated content is deleted, and the DVR window starts filling from the current moment.

DVR reset may be needed in the following situations:
- After technical stream failures
- To clear buffer after test stream launch
- When changing content within one stream
- If accumulation needs to start from a specific moment
Important!
- DVR reset cannot be undone
- After reset, viewers won't be able to return to previously broadcast content
- New accumulation begins immediately after reset
- DVR window size remains the same
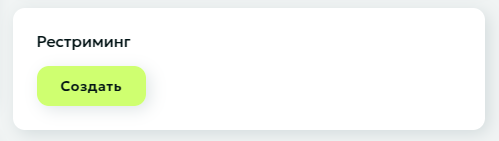
Restream
This section allows you to configure restreaming.
When you publish a stream to our media server (or we pull a stream from your server), we can forward it to other streaming platforms that you specify in the restreaming settings.
For more detailed information, see here.
Broadcast Page
The Broadcast Page provides a ready-to-use webpage with an embedded player for viewing your stream.

To get started click the "Get link" button in the "Broadcast page" section to create a unique URL.
Use the buttons next to the URL to:
- Copy the URL to clipboard
- Regenerate URL if needed
Password Protection
After generating the Broadcast Page Link, you can enable password protection to restrict access:
- Password changes take effect within 30 seconds
- Viewers will be prompted with a password entry form when accessing the page
- Stream playback becomes available only after entering the correct password
This functionality enables access control for your stream and allows sharing the URL with a specific audience only.
SRT-publish
Overview
SRT (Secure Reliable Transport) is a modern protocol specifically designed for reliable video transmission over the internet.
SRT advantages:
- Enhanced reliability with poor connection quality
- Built-in data encryption
- Automatic network condition adaptation
- Minimal transmission delay
Connection Setup
The "Instructions" section contains all necessary data for starting a stream:
- Stream latency selection
- DVR (playback) depth selection
- Publishing and viewing stream links
You can select the stream latency:
- Standard - optimal mode for most streams
- Low - reduced latency (most viewers will experience less than 10 sec latency)
DVR (playback) is the ability to rewind a stream even while it's live. Viewers can start watching from the beginning or return to missed moments. DVR is available for streams with standard latency. You can select the DVR depth from the dropdown menu. Maximum depth is 12 hours.
The system automatically generates necessary data for publishing:
- Primary publishing URL
- Backup URL for additional reliability
Videoplayer
After receiving publishing links and configuring the encoder, we recommend testing the stream for proper operation.
You can view your stream on the stream editing page in the player block.

Clicking the "Configure" button under the player will redirect you to the player settings page, where you can choose your preferred viewing method: viewing created streams separately or all streams together in one player. Below the viewing method selection form, you can find the playlist link and code for embedding the player on your web page.
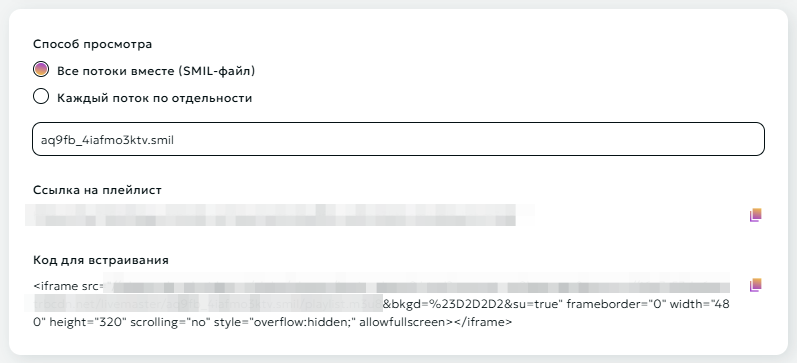
Attention
Use the "Code for embedding" frame to place the player on your resource.
Streaming configuration
Advanced broadcasting settings are available in the "Streaming configuration" block.
Stream Settings
You can create up to 10 streams of different quality
- Open the "Streaming configuration" section
- Use the "Add Stream" button to create a new stream
- For each stream specify:
- Clear name for easy management
- Resolution from the provided list
- Remove unused streams if necessary
- Save changes after configuration

Transcoding $
Transcoding is necessary for creating multibitrate streams. As output, you get several streams of different quality, allowing users to manually select their preferred option or leave adaptive streaming, which automatically adjusts based on the user's bandwidth. This eliminates buffering issues for viewers with slow internet and improves user experience.
To configure transcoding:
- Select appropriate transcoding package
- Save settings
To deactivate transcoding, click again on your selected transcoding package, then click the "Save" button at the bottom of the page.
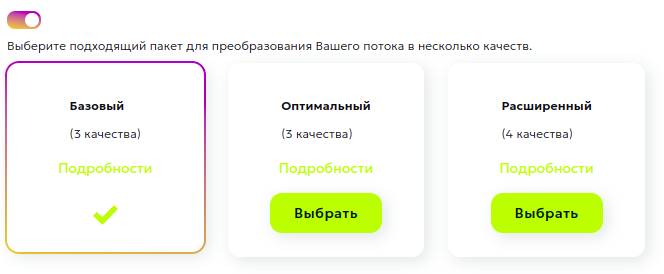
Important transcoding considerations:
- Only one input stream can be used
- Various packages with different processing parameters are available
- The system will automatically create streams of different quality
Stream Recording $
The Stream Recording feature enables archiving of live broadcasts for subsequent use.
Key Features:
- Automatic selection of maximum available quality
- Downloads accessible via the Records page
- 14-day retention period for records
- Option to transfer to Media Storage for extended retention and processing
Operational Flow:
- Activate the recording switch in stream settings
- Recording initiates automatically upon stream detection
- Stream Interruption Protocol:
- System maintains 10-minute reconnection window
- Recording continues to same file if stream resumes within window
- Stream designated as complete after 10-minute timeout
Attention
- Single record file capacity: 12 hours. System automatically generates new file upon reaching capacity
- Default retention period: 14 days from creation
Records Management Interface
The Records page provides access to recorded streams and essential reference information.
Interface functionality includes:
- Comprehensive record content viewer
- File download capability
- Media Storage transfer function
- Monthly recording usage metrics
Content Access Restrictions $
In this section, you can set content distribution restrictions based on:
- Country and region
- IP address
- Referer
- User-Agent
- Authorization restrictions
Module Configuration Process
- Activate the type of restriction you need and choose the default rule (deny or allow).
- Add exceptions to the default rule. For geo-restrictions, also select a rule for the exception itself. This way, you can, for example, deny traffic for an entire country while allowing it for a specific region.
- If necessary, set time intervals for the rule's validity. Intervals should not overlap.
- It's possible to add several different rules of each type, provided their time intervals do not overlap.
Authorization by Secret Key
Description:
Authorization of user requests is performed exclusively in the CDN network, external resources are not used. The decision to access a stream is made by means of our network based on the criteria specified by the content owner:
- Secret key. It is checked that the link was generated by the content owner.
- The URI of the requested stream. It is checked that the link was generated specifically for this stream.
- User's IP address (optional). It is checked that the stream was requested from exactly the IP address for which the link was generated. You can disable the check by selecting the "Do not impose IP address filter" option.
- The expiration time of the link (optional). You can turn off the check by selecting the "Do not impose time restrictions" option.
At the moment the user accesses a protected stream, the content owner needs to generate a special link.
Example:
http://example.a.trbcdn.net/md5(HucJ8tJFjy97yuox2OycOQ,1704067200)/path/to/stream/playlist.m3u8
The link contains authorization parameter md5(<md5 hash>[,<expires>]):
<md5 hash>- MD5 hash in Base64 format for URL, generated based on secret key, URI of the requested stream, user's IP address (optional) and link lifetime (optional);<expires>is the expiration time of the link in POSIX time format (optional).
When accessing content using the generated link, the CDN calculates the MD5 value and compares it with the received one.
If the MD5 value does not match, then a 403 Forbidden response is returned to the user (access is denied).
If the current time exceeds the value <expires>, then a response with the code 410 Gone (the target stream is no longer available) is returned to the user.
Algorithm for generating an MD5 hash (<md5_hash>) for signing links:
- Form the signature string
<secret_word><path_to_stream><ip><expire_time>. The<ip>and/or<expire_time>elements are not added to the signature string ifDo not impose IP address filterand/orDo not impose time restrictionsis specified in the local authorization settings. - Generate
base64_urlviabase64_url(md5(<signature string>)). - Generate the
<md5 hash>signature by performing the following substitutions inbase64_url:- replace the
=character with the empty string''. - replace the
+character with- - replace the
/character with_
- replace the
- Form the link using the obtained signature
<md5 hash>.
Attention
- The domain part of the URI is not used when calculating the hash!
- You can sign part of the path (for example, for /path/to/stream, you can sign the stream itself, /path/to, /path)
- When generating MD5, the URL should not contain urlencoded characters, but should contain the original characters: cyrillic, spaces, percentages, etc. Then you should request the urlencoded version of the URL with this hash.
- The MD5 hash calculated for HTTP is the baseline for this stream. The same hash will be used for links to a stream over the HTTP, HTTPS protocols, despite the fact that the URI for different protocols may differ slightly.
Example of link generation:
-
There are the following input data:
- Secret key:
zah5Mey9Quu8Ea1k - User IP address:
1.2.3.4 - Stream URI:
http://example.a.trbcdn.net/path/to/stream/playlist.m3u8 - Expiration time of the link:
1704067200
- Secret key:
-
Form the signature string
<secret_word><path_to_stream><ip><expire_time>. Let's assume that we include both IP address and link expiration time.Then the signature string looks like this:
zah5Mey9Quu8Ea1k/path/to/stream1.2.3.41704067200 -
Generate
<md5 hash>:PHP example:
$ php -r 'print str_replace("=", "",strtr(base64_encode(md5("zah5Mey9Quu8Ea1k/path/to/stream1.2.3.41704067200", TRUE)), "+/", "-_")) . "\n";' HucJ8tJFjy97yuox2OycOQ#!/usr/bin/python3 import base64 import hashlib secret_word = 'zah5Mey9Quu8Ea1k' path = '/path/to/stream' ip_address = '1.2.3.4' expiration_timestamp = 1704067200 def generate_local_signature(secret_word, path, ip_address=None, timestamp=None): string_to_sign = f'{secret_word}{path}' if ip_address is not None: string_to_sign = f'{string_to_sign}{ip_address}' if timestamp is not None: string_to_sign = f'{string_to_sign}{timestamp}' hashed_string = hashlib.md5(string_to_sign.encode()).digest() decoded_base64_string = base64.b64encode(hashed_string).decode() local_signature = decoded_base64_string.replace('+', '-').replace('/', '_').replace('=', '') return local_signature print(generate_local_signature(secret_word, path, ip_address, expiration_timestamp)) # HucJ8tJFjy97yuox2OycOQPython example:
-
Result link:
http://example.a.trbcdn.net/md5(HucJ8tJFjy97yuox2OycOQ,1704067200)/path/to/stream/playlist.m3u8
External Script Authorization
External authorization is designed to be able to restrict access to the stream with custom logic described in your authorization script. A decision to access the stream is made based on response of your script.
If the authorization script responded with status code = 200, then access to the stream is allowed. Otherwise, access is denied.
The following headers are passed to the authorization script:
- Host: contains the domain name of the server for which the request is intended;
- X-Request-URI: contains the URI of the requested stream;
- X-Forwarded-For: contains the real IP address of the user;
- X-Remote-Addr: contains the IP address of the user or the proxy server.
DVR (Live Stream Playback)
The DVR reset (button "Reset stored DVR") allows clearing the accumulated stream buffer and starting to form it anew. During reset, all previously accumulated content is deleted, and the DVR window starts filling from the current moment.

DVR reset may be needed in the following situations:
- After technical stream failures
- To clear buffer after test stream launch
- When changing content within one stream
- If accumulation needs to start from a specific moment
Important!
- DVR reset cannot be undone
- After reset, viewers won't be able to return to previously broadcast content
- New accumulation begins immediately after reset
- DVR window size remains the same
Restream
This section allows you to configure restreaming.
When you publish a stream to our media server (or we pull a stream from your server), we can forward it to other streaming platforms that you specify in the restreaming settings.
For more detailed information, see here.
Broadcast Page
The Broadcast Page provides a ready-to-use webpage with an embedded player for viewing your stream.

To get started click the "Get link" button in the "Broadcast page" section to create a unique URL.
Use the buttons next to the URL to:
- Copy the URL to clipboard
- Regenerate URL if needed
Password Protection
After generating the Broadcast Page Link, you can enable password protection to restrict access:
- Password changes take effect within 30 seconds
- Viewers will be prompted with a password entry form when accessing the page
- Stream playback becomes available only after entering the correct password
This functionality enables access control for your stream and allows sharing the URL with a specific audience only.
HLS-pull
Overview
With this method, content is loaded into the distribution server's cache from the source server upon the first user request and is used to serve subsequent requests. Objects are stored in the cache for a specified period.
This method is suitable if you have an existing stream in the following protocols:
- Adobe HDS
- Apple HLS
- Microsoft Smooth Streaming (MSS)
Stream format transformation is not performed with this method.
Videoplayer
After configuring the resource, you can verify the broadcast functionality. The switch allows you to view both the source and output streams.

Clicking the "Configure" button below the player redirects you to the player settings page, where you can specify the stream URL for testing. Here you can also find the final playlist link and the code for embedding the player on your webpage.
Please note
Use the "Embed Code" frame to place the player on your resource.
Streaming configuration
The "Streaming configuration" block provides access to advanced broadcasting settings. Here you can fine-tune various parameters of your stream.
Data Source
If you have multiple content sources (primary/backup), you can add them to a Domain Group and configure the priority for each. If the "highest priority" source becomes unavailable, the CDN network will automatically switch to the next source. It will automatically switch back to the priority source once it's functioning normally again.
You can configure Weight and Max fails for each source.
-
Weight is a numerical value that determines what proportion of requests a specific server should receive. The higher the weight, the more requests will be directed to that server. The default weight is 1.
-
Max_fails - this parameter defines the number of failed connection attempts to a server, after which Nginx will consider it unavailable for a certain period. The default max_fails value is 10.
Use HTTPS When Requesting Sources
By default, requests to sources are made using HTTPS. Here you can disable the use of HTTPS if needed.
You can also enable source certificate verification by selecting the corresponding option.
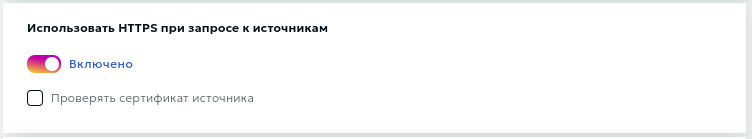
Please note
The "Verify source certificate" option is only available when "Use HTTPS for source requests" is enabled.
Specifying an SNI Host
The additional option to specify an SNI host (Server Name Indication) allows you to manually define the hostname sent during the TLS handshake with the origin server. This functionality is particularly useful in the following cases:
- When using virtual hosting, where a single IP address serves multiple domains
- When non-standard configurations are required for specific hosts
- To ensure proper handling of SSL/TLS certificates in multiple-domain configurations. For example, if your origin server hosts both 'example.com' and 'example.net' on the same IP address, specifying the SNI host ensures that the correct SSL/TLS certificate is presented during the handshake.
Hostname When Requesting Source
If you're using hosting services such as Wix, Amazon S3, Selectel, etc., please pay special attention to the Hostname section.
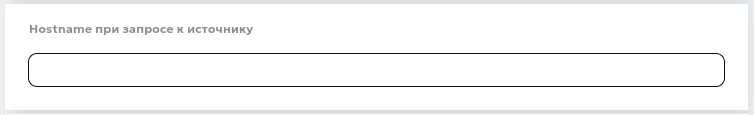
Many virtual hosting services (such as Amazon S3) host multiple websites on a single web server. For CDN nodes to access your content correctly, you need to specify the correct Hostname.
Follow these steps if you're unsure about your Hostname:
- Visit your website and right-click on any image to copy its link.
- Paste this link into a new browser window. The resulting domain is your site's Content Source. For example, if your site is hosted on Wix, the content source domain will be static.wixstatic.com
- Go to https://check-host.net and enter your website's domain (not the content source domain).
- On the "Information" tab, look for the "Resource Name" - this is your Hostname. For instance, if you're using Amazon hosting, your Hostname might look like: ec7-54-151-126-156.eu-west-1.compute.amazonaws.com
- Enter this Hostname in your account dashboard
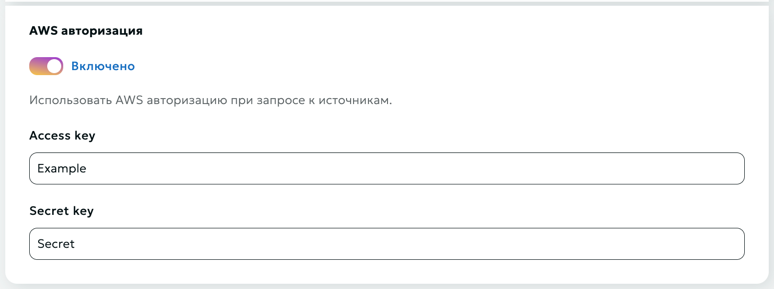
AWS Authorization
You can use AWS authorization when requesting from sources. To do this, select the corresponding option and enter two keys: the access key and the secret key.
Caching
Here you can specify caching times based on response codes (2xx, 3xx, 4xx, 5xx) and set the option to ignore caching control headers ("Expires" and "Cache-Control").
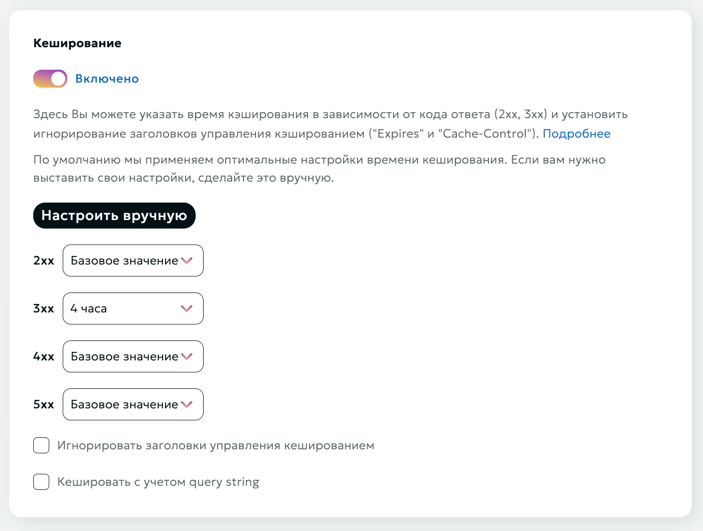
Initially, each user has basic time settings, but these can be customized.
Important
The cache duration settings are specified in seconds
Ignore caching control headers
If the content source (origin) responses already contain Cache-Control and/or Expires headers, caching is performed for the time specified in these headers.
To change this behavior, enable Ignore caching control headers.
In this case, caching will be performed for the time specified in this section.
The specified caching time will also be used for content source (origin) responses that do not contain caching control headers.
Please note
Invalid header values (Expires with a past time, or Cache-control: private) disable caching, which often leads to increased load on the content source (origin).
Using Stale Content in CDN
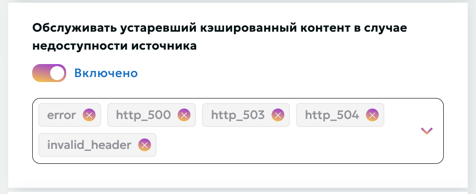
The Use Stale option allows the CDN to serve previously cached versions of content when fetching up-to-date data from the origin server is not possible. This functionality ensures continuous content availability and helps minimize service disruptions for users.
When the "Serve Stale Content on Origin Unavailability" option is enabled, the system will return cached content in the following cases:
- error - an error occurred while establishing a connection with the server, passing a request to it, or reading the response header.
- timeout - a timeout has occurred while establishing a connection with the server, passing a request to it, or reading the response header.
- invalid_header - a server returned an empty or invalid response.
- updating - permits using a stale cached response if it is currently being updated.
- http_500 - a server returned a response with the code 500.
- http_502 - a server returned a response with the code 502.
- http_503 - a server returned a response with the code 503.
- http_504 - a server returned a response with the code 504.
In these scenarios, the user will receive the most recent cached version of the requested resource instead of an error message. This provides a better user experience during temporary issues with the origin server.
Stale conditions
Here you can set a list of conditions to give outdated cached content if the origin is unavailable (the enabled Use Stale setting is required).
List of available options:
- error - an error occurred while establishing a connection with the server, passing a request to it, or reading the response header.
- timeout - a timeout has occurred while establishing a connection with the server, passing a request to it, or reading the response header.
- invalid_header - a server returned an empty or invalid response.
- updating - permits using a stale cached response if it is currently being updated.
- http_500 - a server returned a response with the code 500.
- http_502 - a server returned a response with the code 502.
- http_503 - a server returned a response with the code 503.
- http_504 - a server returned a response with the code 504.
- http_403 - a server returned a response with the code 403.
- http_404 - a server returned a response with the code 404.
- http_429 - a server returned a response with the code 429.
Cache considering query string
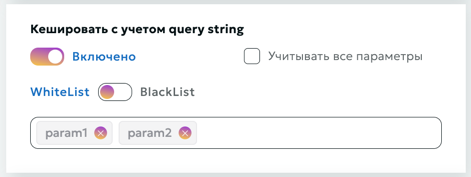
When this option is enabled, query string parameters will be taken into account when caching content.
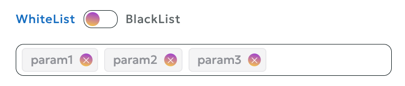
Query string whitelist
The Query String Whitelist defines a list of allowed query parameters (request arguments), which are taken into account when caching. Any query parameters not included in this list are ignored during request processing.
Warning
By default, the Query String Whitelist is empty, meaning that all query string parameters in the request are included in cache key generation and processing.
Query string blacklist
The Query String Blacklist defines a list of disabled query parameters (request arguments), which are taken into account when caching. Any query parameters included in this list are ignored during request processing.
Warning
By default, the Query String Blacklist is empty, meaning that all query string parameters in the request are included in cache key generation and processing.
If you want to redefine whitelist/blacklist, then you need to disable the option "Consider all query string parameters" and set parameter lists.
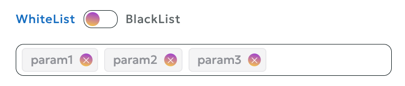
Warning
You can set only one of the 2 properties: either whitelist or blacklist.
Cache Based on Cookies
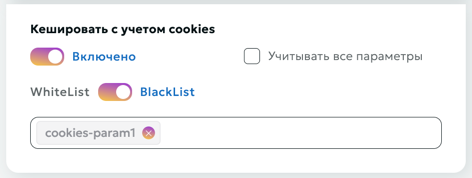
When the "Cache Based on Cookies" option is enabled, the system will take cookie parameters into account when caching content. This allows for the creation of separate cache versions for different cookie values.
Cookies Whitelist
The Cookies Whitelist allows you to specify a list of cookies that should be considered during caching and other cookie-related operations. All other cookies not included in this list are ignored by the system.
Warning
By default, the Cookies Whitelist is empty, meaning that all cookie parameters are included in cache key generation and request processing
Cookies Blacklist
The Cookies Blacklist allows you to specify a list of cookies that should be not considered during caching and other cookie-related operations. All other cookies included in this list are ignored by the system.
Warning
By default, the Cookies Blacklist is empty, meaning that all cookie parameters are included in cache key generation and request processing
If you want to redefine whitelist/blacklist, then you need to disable the option "Consider all parameters" and set parameter lists.
Warning
You can set only one of the 2 properties, either whitelist or blacklist.
This approach helps:
- Avoid cache redundancy
- Retain only the necessary data for personalization
- Optimize storage of dynamic content
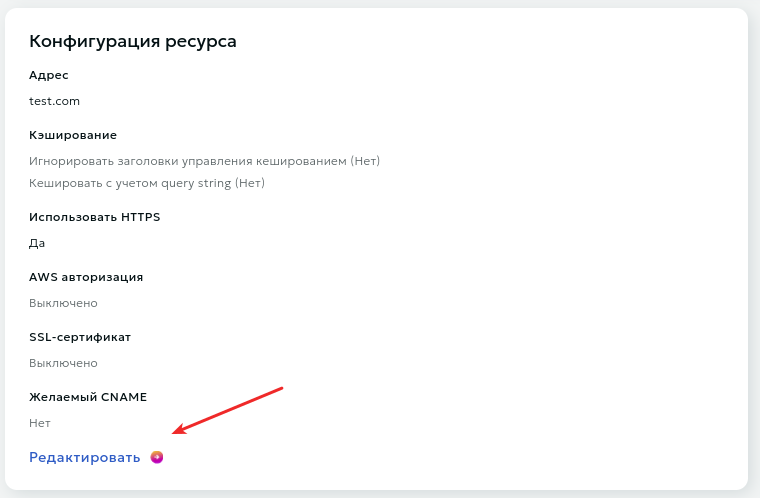
CNAME
A CNAME record allows you to assign an alias to a host. This alias typically associates a specific function with the host or simply shortens its name.
By default, your content is accessible at: example.a.trbcdn.net/images/1.jpg
With CNAME, you can set up access at: cdn.example.com/images/1.jpg
-
Creating a CNAME record:
- Open the DNS management page on your DNS hosting site
- Create a new CNAME record with the following parameters:
- Name (Host): "cdn" Note: Some control panels may require you to specify the full subdomain name, e.g., cdn.example.com
- Value: example.a.trbcdn.net. (note the period at the end)
-
Waiting for changes to apply:
- DNS changes may take up to 72 hours to take effect
-
Verifying the setup:
- After the waiting period, check if your content is accessible at the new address
- Use DNS checking tools to confirm the correct setup
HTTPS Distribution via CNAME (SSL Certificate)
By default, after saving the settings, your content will be accessible via HTTPS
The standard URL will look like: https://example.a.trbcdn.net
If you plan to use an SSL certificate, you have two main options:
a) Upload your own certificate:
- Prepare your SSL certificate in advance
- Upload it before or after creating the resource
- Select the uploaded certificate from the list of available ones when configuring the resource
b) Issue a Let's Encrypt certificate:
- Choose the option to issue a Let's Encrypt certificate in the resource settings
- The system will automatically generate and configure the certificate for your resource
Content Access Restrictions $
In this section, you can set content distribution restrictions based on:
- Country and region
- IP address
- Referer
- User-Agent
- Authorization restrictions
Module Configuration Process
- Activate the type of restriction you need and choose the default rule (deny or allow).
- Add exceptions to the default rule. For geo-restrictions, also select a rule for the exception itself. This way, you can, for example, deny traffic for an entire country while allowing it for a specific region.
- If necessary, set time intervals for the rule's validity. Intervals should not overlap.
- It's possible to add several different rules of each type, provided their time intervals do not overlap.
Authorization by Code Word
Description:
Authorization of user requests is performed exclusively in the CDN network, external resources are not used. The decision to access a stream is made by means of our network based on the criteria specified by the content owner:
- Secret key. It is checked that the link was generated by the content owner.
- The URI of the requested stream. It is checked that the link was generated specifically for this stream.
- User's IP address (optional). It is checked that the stream was requested from exactly the IP address for which the link was generated. You can disable the check by selecting the "Do not impose IP address filter" option.
- The expiration time of the link (optional). You can turn off the check by selecting the "Do not impose time restrictions" option.
At the moment the user accesses a protected stream, the content owner needs to generate a special link.
Example:
http://example.a.trbcdn.net/md5(HucJ8tJFjy97yuox2OycOQ,1704067200)/path/to/stream/playlist.m3u8
The link contains authorization parameter md5(<md5 hash>[,<expires>]):
<md5 hash>- MD5 hash in Base64 format for URL, generated based on secret key, URI of the requested stream, user's IP address (optional) and link lifetime (optional);<expires>is the expiration time of the link in POSIX time format (optional).
When accessing content using the generated link, the CDN calculates the MD5 value and compares it with the received one.
If the MD5 value does not match, then a 403 Forbidden response is returned to the user (access is denied).
If the current time exceeds the value <expires>, then a response with the code 410 Gone (the target stream is no longer available) is returned to the user.
Algorithm for generating an MD5 hash (<md5_hash>) for signing links:
- Form the signature string
<secret_word><path_to_stream><ip><expire_time>. The<ip>and/or<expire_time>elements are not added to the signature string ifDo not impose IP address filterand/orDo not impose time restrictionsis specified in the local authorization settings. - Generate
base64_urlviabase64_url(md5(<signature string>)). - Generate the
<md5 hash>signature by performing the following substitutions inbase64_url:- replace the
=character with the empty string''. - replace the
+character with- - replace the
/character with_
- replace the
- Form the link using the obtained signature
<md5 hash>.
Attention
- The domain part of the URI is not used when calculating the hash!
- You can sign part of the path (for example, for /path/to/stream, you can sign the stream itself, /path/to, /path)
- When generating MD5, the URL should not contain urlencoded characters, but should contain the original characters: cyrillic, spaces, percentages, etc. Then you should request the urlencoded version of the URL with this hash.
- The MD5 hash calculated for HTTP is the baseline for this stream. The same hash will be used for links to a stream over the HTTP, HTTPS protocols, despite the fact that the URI for different protocols may differ slightly.
Example of link generation:
-
There are the following input data:
- Secret key:
zah5Mey9Quu8Ea1k - User IP address:
1.2.3.4 - Stream URI:
http://example.a.trbcdn.net/path/to/stream/playlist.m3u8 - Expiration time of the link:
1704067200
- Secret key:
-
Form the signature string
<secret_word><path_to_stream><ip><expire_time>. Let's assume that we include both IP address and link expiration time.Then the signature string looks like this:
zah5Mey9Quu8Ea1k/path/to/stream1.2.3.41704067200 -
Generate
<md5 hash>:PHP example:
$ php -r 'print str_replace("=", "",strtr(base64_encode(md5("zah5Mey9Quu8Ea1k/path/to/stream1.2.3.41704067200", TRUE)), "+/", "-_")) . "\n";' HucJ8tJFjy97yuox2OycOQ#!/usr/bin/python3 import base64 import hashlib secret_word = 'zah5Mey9Quu8Ea1k' path = '/path/to/stream' ip_address = '1.2.3.4' expiration_timestamp = 1704067200 def generate_local_signature(secret_word, path, ip_address=None, timestamp=None): string_to_sign = f'{secret_word}{path}' if ip_address is not None: string_to_sign = f'{string_to_sign}{ip_address}' if timestamp is not None: string_to_sign = f'{string_to_sign}{timestamp}' hashed_string = hashlib.md5(string_to_sign.encode()).digest() decoded_base64_string = base64.b64encode(hashed_string).decode() local_signature = decoded_base64_string.replace('+', '-').replace('/', '_').replace('=', '') return local_signature print(generate_local_signature(secret_word, path, ip_address, expiration_timestamp)) # HucJ8tJFjy97yuox2OycOQPython example:
-
Result link:
http://example.a.trbcdn.net/md5(HucJ8tJFjy97yuox2OycOQ,1704067200)/path/to/stream/playlist.m3u8
Authorization by External Script
External authorization is designed to be able to restrict access to the stream with custom logic described in your authorization script. A decision to access the stream is made based on response of your script.
If the authorization script responded with status code = 200, then access to the stream is allowed. Otherwise, access is denied.
The following headers are passed to the authorization script:
- Host: contains the domain name of the server for which the request is intended;
- X-Request-URI: contains the URI of the requested stream;
- X-Forwarded-For: contains the real IP address of the user;
- X-Remote-Addr: contains the IP address of the user or the proxy server.
Additional content distribution areas $
This option allows you to configure content delivery parameters beyond the main service area.

Connection
- Switch the toggle to
Turned on - Select one or more zones:
- EMEA (Europe, Middle East, and Africa)
- APAC (Asia-Pacific)
- AM (Americas)
- Click the
Applybutton - Wait for some time while the settings are applied to the network
HTTPS Configuration
- Enable HTTPS distribution in the additional zones settings
- Select a certificate from the list of existing ones or upload a new one
Important!
When updating the SSL certificate in the main resource, the certificate in additional distribution zones is not automatically updated. You need to manually update the certificate in the additional zones settings.
When receiving a new certificate:
- Update the certificate in the main resource settings
- Update the certificate in the additional distribution zones settings
Expert settings
Attention!
This section is intended for advanced users and allows for fine-tuning of the CDN resource.
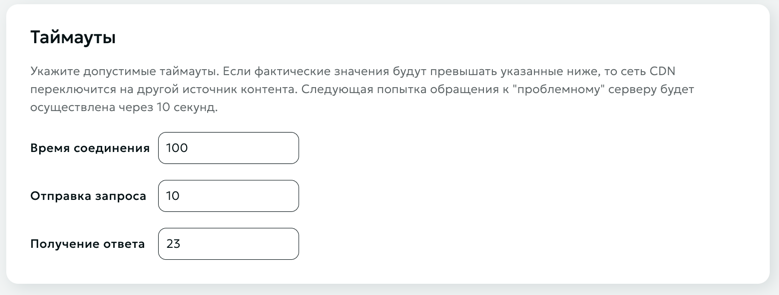
Timeouts
In this section, you can specify acceptable timeouts for CDN nodes when accessing your origin. If the actual values start to exceed the acceptable ones, a switch to another content source specified in the Data Source section will occur.
Use HTTP3
By default, the HTTP/2.0 protocol is supported. Enable this option if HTTP3 support is required.
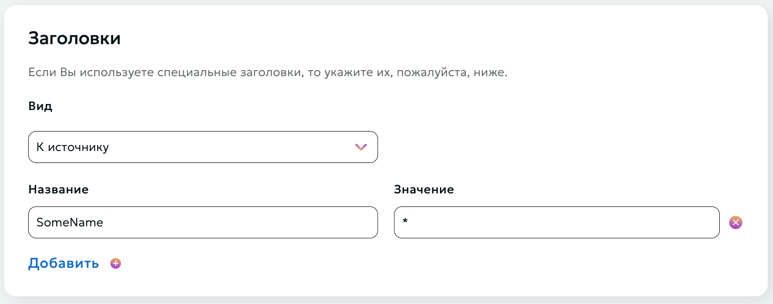
Headers
In this section, you can specify special headers that need to be added when accessing the data source (To source), or when delivering content to end users (For client).
Hide-in-response option
The Hide-in-response option is used to remove specific HTTP headers from the response sent to the client, which can help improve security or reduce unnecessary information exposure.
CORS Check on CDN Side
Description
In some cases, a browser may treat a request to access to certain content hosted on a CDN network as a cross-domain request and block it. It is primarily related to fonts. The issue is addressed by setting CORS (Cross-Origin Resource Sharing) headers for cached objects.
There are two options:
- You can set CORS headers on the origin server and disable their verification in our network yourself.
- You can set up CORS verification in the Your Account section in our network.
Setup in Dashboard
The CORS verification procedure provided for configuration is based on our proprietary module operation. Its functionality is based on W3C recommendations.
Module Operation Fundamentals:
-
Where CORS is enabled, Access-Control-* headers from the origin are always ignored and excluded from the response.
-
Any request without Origin header is not a cross-resource request, and Access-Control-* headers are not transmitted to the client.
-
Our module never adds Access-Control-Request-* headers, since they are incoming request headers generated by the browser, same as Origin.
-
Where there is an Origin header, its contents will be matched against that set by the user. In the absence of restrictions, the Access-Control-Allow-Origin response header will include "*", while where there are any restrictions and where Origin is on the allowed list, then ACAO will include http(s?)://${http_origin}; otherwise, the response will include Access-Control-* headers.
-
Access-Control-Expose-Headers headers are added, if such headers are set by the user. By default, we state a permission to access Content-Range for the operation of range-requests (for JS-based players).
-
Access-Control-Allow-Credentials (ACAC) headers are included in accordance to that set by the user.
-
Access-Control-Allow-Methods, Access-Control-Allow-Headers, and Access-Control-Max-Age headers are included only in a response to a request based on the OPTIONS method, which is processed locally and not forwarded to the origin.
-
Access-Control-Allow-Methods header is set to be equal to the contents of the Access-Control-Request-Method header, if such header is present and is on the list of simple requests (GET, HEAD, POST), or a list set by the user. Where the method is not on the allowed list, then the response will not include Access-Control-* headers. If a request does not contain Access-Control-Request-Method, no Access-Control-Allow-Methods will be set.
-
Access-Control-Allow-Headers is set to be equal to the contents of the Access-Control-Request-Headers header, if such header is present, Access-Control-Request-Method request header is present, and all headers are on the list of simple headers (Accept, Accept-Language, Content-Type, Content-Language) or on the user-set list. Where at least one header is not on the allowed list, then the response will not contain Access-Control-* headers. Where a request does not contain Access-Control-Request-Method and Access-Control-Request-Headers, Access-Control-Allow-Headers will not be stated.
-
Access-Control-Max-Age header will be stated in accordance with that set by the user, but not by default.
-
Any additional response header, specified by the client, will be added/overridden after CORS module processing, while, for example, Access-Control-Allow-Origin: * in header sections will be added irrespective of the CORS module operation results.
Module Configuration Process
CORS verification is active by default. If CORS authorization is disabled, all preflight requests will be forwarded to your origin. The headers, described above and set on the origin, will not be affected and will be transmitted unchanged to end users.
You may adjust the module operation by setting the following parameters:
Allowed Domains (not verified by default, all domains are allowed)
Values may set by either of the following methods:
- example.com – exact match
- *.example.com - all subdomains example.com exclusive of example.com
- .example.com – all Level 3 domains inclusive of example.com
- ~a\d+\.example.com – regular expression
Secure Request Headers
Cache-Control, Content-Language, Content-Type, Expires, Last-Modified, Pragma are allowed by default. You may add your headers to this list.
Upper Level API Accessible Headers (Expose Headers)
Cache-Control, Content-Language, Content-Type, Expires, Last-Modified, Pragma are allowed by default. You may add your headers to this list.
Safe Methods
GET, HEAD, POST are allowed by default. You may add your methods to this list.
Access-Control-Allow-Credentials Header
Cookies, sessions, authorizations are incompatible with caching services due to their operating logic. However, if you need to set an Access-Control-Allow-Credentials header, you can do it.
Preflight Request Response Lifetime
A period of time during which a response to a Preflight request is deemed to be relevant.
Attention!
Irrespective of whether CORS authorization is enabled/disabled and its operation results, you may manually redefine any header for responses to end users. To this end, specify its name and desired value in "Headers" section. Authorization header value will be substituted with that specified by you after the CORS verification stage completion.
Rules
This section is designed for finer control of CDN network operation. Individual rules for any section/path allow managing headers, caching, CORS, authorization, and other parameters.
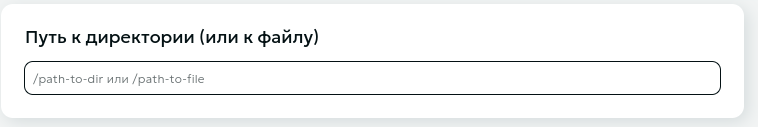
Rule Creation
To create a rule, specify the path to the directory or specific file to which this rule should be applied.
Please note
When configuring rules, it is important to remember that the characters ~ or ~* must be specified to use regular expressions in the path.
~is used to define case-sensitive matching~*is used to define case-insensitive matching
Rule Configuration
Rule configuration is set up similarly to the configuration for the entire resource.
Headers, content access restrictions, and CORS verification for specific paths (rules) are configured similarly to the options for the entire resource.
HTTP Response Status Configuration
In this option, you can configure special rules for returned HTTP statuses. The following configuration options are available:
- Status Code and Response Text:
- Specify the HTTP status to return
- Optionally add text to be sent in the response body
- Status Code and Redirection:
- For redirection codes (301, 302, 303, 307, 308), specify the URL where the user will be directed
- URL can be either absolute (starting with http:// or https://) or relative
RTMP/RTSP/SRT-pull
Instruction
The "Instructions" section contains all necessary data for starting a stream:
- Stream latency selection
- DVR (playback) depth selection
- Viewing stream links
You can select the stream latency:
- Standard - optimal mode for most streams
- Low - reduced latency (most viewers will experience less than 10 sec latency)
DVR (playback) is the ability to rewind a stream even while it's live. Viewers can start watching from the beginning or return to missed moments. DVR is available for streams with standard latency. You can select the DVR depth from the dropdown menu. Maximum depth is 12 hours.
Videoplayer
You can view your stream on the stream editing page in the player block.

Clicking the "Configure" button under the player will redirect you to the player settings page, where you can choose your preferred viewing method: viewing created streams separately or all streams together in one player. Below the viewing method selection form, you can find the playlist link and code for embedding the player on your web page.
Attention
Use the "Code for embedding" frame to place the player on your resource.
Streaming configuration
In the "Streaming configuration" section, you can set up pull parameters and configure advanced broadcasting settings.
Stream Settings
In this section, you can configure the pull parameters for streams of different quality.
- Open the "Streaming configuration" section
- Use the "Add Stream" button to create a new stream
- For each stream specify:
- Clear name for easy management
- Resolution from the provided list
- Primary address
- Backup address
- Remove unused streams if necessary
- Save changes after configuration
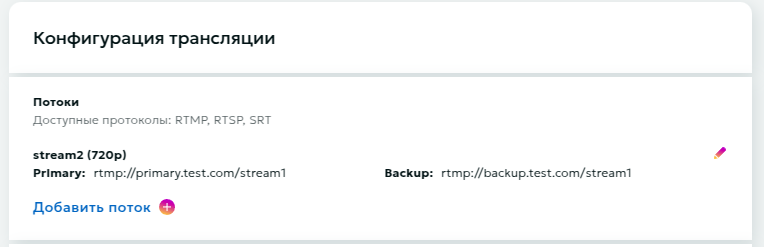
Please note
Available protocols: RTMP, RTSP, SRT
Transcoding
Transcoding is necessary for creating multibitrate streams. As output, you get several streams of different quality, allowing users to manually select their preferred option or leave adaptive streaming, which automatically adjusts based on the user's bandwidth. This eliminates buffering issues for viewers with slow internet and improves user experience.
To configure transcoding:
- Select appropriate transcoding package
- Save settings
To deactivate transcoding, click again on your selected transcoding package, then click the "Save" button at the bottom of the page.
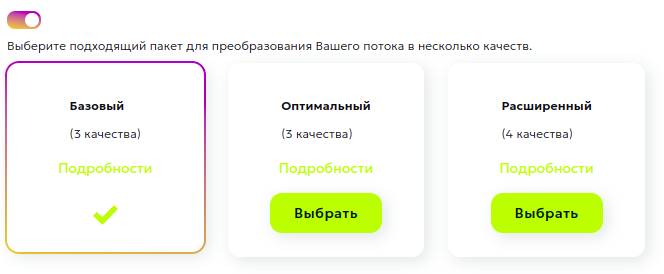
Important transcoding considerations:
- Only one input stream can be used
- Various packages with different processing parameters are available
- The system will automatically create streams of different quality
Stream Recording
The Stream Recording feature enables archiving of live broadcasts for subsequent use.
Key Features:
- Automatic selection of maximum available quality
- Downloads accessible via the Records page
- 14-day retention period for records
- Option to transfer to Media Storage for extended retention and processing
Operational Flow:
- Activate the recording switch in stream settings
- Recording initiates automatically upon stream detection
- Stream Interruption Protocol:
- System maintains 10-minute reconnection window
- Recording continues to same file if stream resumes within window
- Stream designated as complete after 10-minute timeout
Attention
- Single record file capacity: 12 hours. System automatically generates new file upon reaching capacity
- Default retention period: 14 days from creation
Records Management Interface
The Records page provides access to recorded streams and essential reference information.
Interface functionality includes:
- Comprehensive record content viewer
- File download capability
- Media Storage transfer function
- Monthly recording usage metrics
Content Access Restrictions
In this section, you can set content distribution restrictions based on:
- Country and region
- IP address
- Referer
- User-Agent
- Authorization restrictions
Module Configuration Process
- Activate the type of restriction you need and choose the default rule (deny or allow).
- Add exceptions to the default rule. For geo-restrictions, also select a rule for the exception itself. This way, you can, for example, deny traffic for an entire country while allowing it for a specific region.
- If necessary, set time intervals for the rule's validity. Intervals should not overlap.
- It's possible to add several different rules of each type, provided their time intervals do not overlap.
Authorization by Secret Key
Description:
Authorization of user requests is performed exclusively in the CDN network, external resources are not used. The decision to access a stream is made by means of our network based on the criteria specified by the content owner:
- Secret key. It is checked that the link was generated by the content owner.
- The URI of the requested stream. It is checked that the link was generated specifically for this stream.
- User's IP address (optional). It is checked that the stream was requested from exactly the IP address for which the link was generated. You can disable the check by selecting the "Do not impose IP address filter" option.
- The expiration time of the link (optional). You can turn off the check by selecting the "Do not impose time restrictions" option.
At the moment the user accesses a protected stream, the content owner needs to generate a special link.
Example:
http://example.a.trbcdn.net/md5(HucJ8tJFjy97yuox2OycOQ,1704067200)/path/to/stream/playlist.m3u8
The link contains authorization parameter md5(<md5 hash>[,<expires>]):
<md5 hash>- MD5 hash in Base64 format for URL, generated based on secret key, URI of the requested stream, user's IP address (optional) and link lifetime (optional);<expires>is the expiration time of the link in POSIX time format (optional).
When accessing content using the generated link, the CDN calculates the MD5 value and compares it with the received one.
If the MD5 value does not match, then a 403 Forbidden response is returned to the user (access is denied).
If the current time exceeds the value <expires>, then a response with the code 410 Gone (the target stream is no longer available) is returned to the user.
Algorithm for generating an MD5 hash (<md5_hash>) for signing links:
- Form the signature string
<secret_word><path_to_stream><ip><expire_time>. The<ip>and/or<expire_time>elements are not added to the signature string ifDo not impose IP address filterand/orDo not impose time restrictionsis specified in the local authorization settings. - Generate
base64_urlviabase64_url(md5(<signature string>)). - Generate the
<md5 hash>signature by performing the following substitutions inbase64_url:- replace the
=character with the empty string''. - replace the
+character with- - replace the
/character with_
- replace the
- Form the link using the obtained signature
<md5 hash>.
Attention
- The domain part of the URI is not used when calculating the hash!
- You can sign part of the path (for example, for /path/to/stream, you can sign the stream itself, /path/to, /path)
- When generating MD5, the URL should not contain urlencoded characters, but should contain the original characters: cyrillic, spaces, percentages, etc. Then you should request the urlencoded version of the URL with this hash.
- The MD5 hash calculated for HTTP is the baseline for this stream. The same hash will be used for links to a stream over the HTTP, HTTPS protocols, despite the fact that the URI for different protocols may differ slightly.
Example of link generation:
-
There are the following input data:
- Secret key:
zah5Mey9Quu8Ea1k - User IP address:
1.2.3.4 - Stream URI:
http://example.a.trbcdn.net/path/to/stream/playlist.m3u8 - Expiration time of the link:
1704067200
- Secret key:
-
Form the signature string
<secret_word><path_to_stream><ip><expire_time>. Let's assume that we include both IP address and link expiration time.Then the signature string looks like this:
zah5Mey9Quu8Ea1k/path/to/stream1.2.3.41704067200 -
Generate
<md5 hash>:PHP example:
$ php -r 'print str_replace("=", "",strtr(base64_encode(md5("zah5Mey9Quu8Ea1k/path/to/stream1.2.3.41704067200", TRUE)), "+/", "-_")) . "\n";' HucJ8tJFjy97yuox2OycOQ#!/usr/bin/python3 import base64 import hashlib secret_word = 'zah5Mey9Quu8Ea1k' path = '/path/to/stream' ip_address = '1.2.3.4' expiration_timestamp = 1704067200 def generate_local_signature(secret_word, path, ip_address=None, timestamp=None): string_to_sign = f'{secret_word}{path}' if ip_address is not None: string_to_sign = f'{string_to_sign}{ip_address}' if timestamp is not None: string_to_sign = f'{string_to_sign}{timestamp}' hashed_string = hashlib.md5(string_to_sign.encode()).digest() decoded_base64_string = base64.b64encode(hashed_string).decode() local_signature = decoded_base64_string.replace('+', '-').replace('/', '_').replace('=', '') return local_signature print(generate_local_signature(secret_word, path, ip_address, expiration_timestamp)) # HucJ8tJFjy97yuox2OycOQPython example:
-
Result link:
http://example.a.trbcdn.net/md5(HucJ8tJFjy97yuox2OycOQ,1704067200)/path/to/stream/playlist.m3u8
External Script Authorization
External authorization is designed to be able to restrict access to the stream with custom logic described in your authorization script. A decision to access the stream is made based on response of your script.
If the authorization script responded with status code = 200, then access to the stream is allowed. Otherwise, access is denied.
The following headers are passed to the authorization script:
- Host: contains the domain name of the server for which the request is intended;
- X-Request-URI: contains the URI of the requested stream;
- X-Forwarded-For: contains the real IP address of the user;
- X-Remote-Addr: contains the IP address of the user or the proxy server.
DVR (Live Stream Playback)
The DVR reset (button "Reset stored DVR") allows clearing the accumulated stream buffer and starting to form it anew. During reset, all previously accumulated content is deleted, and the DVR window starts filling from the current moment.

DVR reset may be needed in the following situations:
- After technical stream failures
- To clear buffer after test stream launch
- When changing content within one stream
- If accumulation needs to start from a specific moment
Important!
- DVR reset cannot be undone
- After reset, viewers won't be able to return to previously broadcast content
- New accumulation begins immediately after reset
- DVR window size remains the same
Restream
This section allows you to configure restreaming.
When you publish a stream to our media server (or we pull a stream from your server), we can forward it to other streaming platforms that you specify in the restreaming settings.
For more detailed information, see here.
Broadcast Page
The Broadcast Page provides a ready-to-use webpage with an embedded player for viewing your stream.

To get started click the "Get link" button in the "Broadcast page" section to create a unique URL.
Use the buttons next to the URL to:
- Copy the URL to clipboard
- Regenerate URL if needed
Password Protection
After generating the Broadcast Page Link, you can enable password protection to restrict access:
- Password changes take effect within 30 seconds
- Viewers will be prompted with a password entry form when accessing the page
- Stream playback becomes available only after entering the correct password
This functionality enables access control for your stream and allows sharing the URL with a specific audience only.